ple on Tuesday asked the U.S. International Trade Commission to block the importation into the country of HTC's Google Android-based mobile phones, including the Google-branded Nexus One.
Apple asked the court for "a permanent exclusion order" that would bar from entry "all mobile communications devices and components" made by HTC that carry the offending technologies, according to court documents.
Apple on Tuesday sued HTC for alleged, multiple patent violations, claiming the Taiwan-based manufacturer's products infringe on its iPhone technology. Apple filed the actions with the ITC and the U.S. District Court for Delaware.
In the ITC filing, Apple says 11 HTC phones violate its patents, including the Nexus One, Touch Pro, Touch Diamond, Pure, Imagio, and myTouch 3G. Apple claims HTC infringed on a total of 20 patents governing a range of technologies.
Apple wants the ITC to block HTC and its partners from "importing, marketing, advertising, demonstrating, warehousing inventory for distribution, distributing, offering for sale" any of the listed phones.
Apple is also seeking unspecified monetary damages in the Delaware court.
"We can sit by and watch competitors steal our patented inventions, or we can do something about it. We've decided to do something about it," said Apple CEO Steve Jobs, in a statement. "We think competition is healthy, but competitors should create their own technology, not steal ours," said Jobs.
Patent suits are not uncommon in the ultra-competitive tech industry, but vendors generally take a low-key approach and let court documents speak for themselves. That Apple issued a press release featuring its high-profile CEO indicates the company views HTC's alleged infringements as a serious competitive threat.
"Apple has been and continues to be damaged by defendants' infringement," Apple said in its filing with the Delaware court. HTC has yet to file a formal response to the allegations.
InformationWeek has published an in-depth report on a data-centric approach to
'IT' 카테고리의 다른 글
| Must-Have iPad Apps For Professionals (0) | 2010.04.09 |
|---|---|
| New Twitter Feature Looks For Malicious URLs (0) | 2010.03.12 |
| IBM Eyes The iPad (0) | 2010.02.19 |
| PayPal to become a way to pay for Facebook ads (0) | 2010.02.19 |
| SoftwareQATest.com (0) | 2010.02.03 |
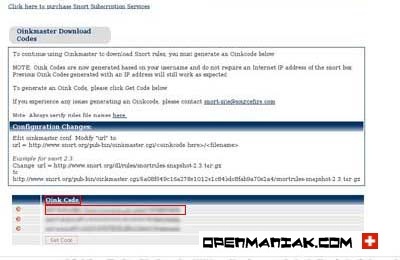
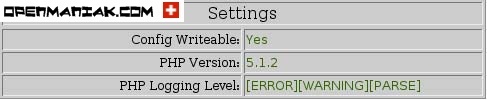
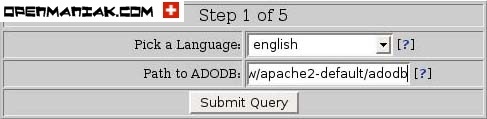
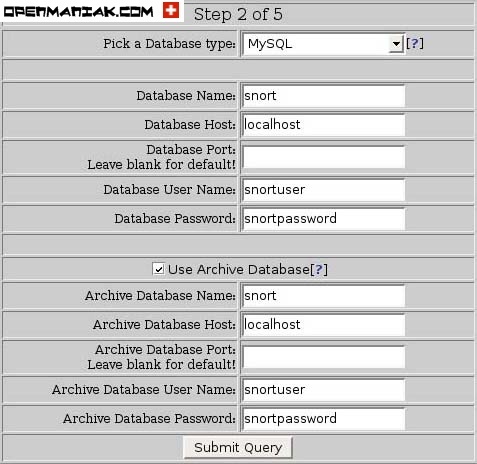
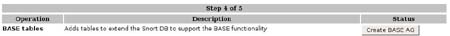
 Install or update the rules.
Install or update the rules.